End point Security
Loosely referred to as Anti Virus , a quality end point solution protects against malwares & protection from cyber threats. We recommend Quick Heal Security. Quick Heal uses the Best Technology , have the distinction of Most Award Winning to deliver the unmatched security with smooth user experience for almost every device - Desktop/ Laptop / Tablet / Mobile.
Endpoint Security Total
Endpoint Security Total is designed to facilitate world-class protection for every system within your enterprise with advanced features such as application control, file activity monitor and more. With this suite you can monitor and safeguard each endpoint while boosting its fine-tuned business impact.
Key Benefits
- Innovative device control to configure access for several device types.
- Advanced web access and data control for comprehensive policy enforcement.
- Smart blocking of unauthorized applications to achieve organizational compliance.
- Proactive scanning of installed applications to detect unforeseen vulnerabilities.
- Detailed insights into every connected endpoint for uniform asset regulation.
Features of Endpoint Security Total
Advanced Device Control
Configures device policies for various device types for Windows and Mac platforms to safeguard the network against unverified devices.
Web Filtering
Websites can be blocked individually or as per categories to limit web access for employees.
Application Control
Categories of applications can be authorized or unauthorized from being executed within the network.
Asset Management
Vigilant monitoring of hardware and software configurations of every endpoint allows administrators to stay in-the-know of any alterations on company systems.
Vulnerability Scan
By scanning known vulnerabilities of applications and operating systems, this feature allows users to update necessary security patches.
Data Loss Prevention*
Secures confidential data and prevents the leakage of business secrets to avoid losses. Data-at-rest can also be scanned on endpoints and removable devices.
File Activity Monitor
Monitors confidential company files and notifies administrators when such files are copied, renamed or deleted.
IDS / IPS Protection
Advanced protection that pro-actively detects and prevents malicious activity which may exploit application vulnerabilities.
Group Policy Management
Administrators can define user groups based on the hierarchy within the organization and set flexible policies as per situational requirements.
Spam Protection
Scans your endpoint inboxes for spam, phishing attacks and unsolicited emails that sneak through network defences.
Browsing Protection
Endpoint clients can be safeguarded against attacks originating from malicious websites accessed from within the network.
Phishing Protection
Phishing attacks that originate from malicious codes over the Internet are thwarted before they can enter the network and spread.
Firewall Protection
Administrators can customize permission-based rules in line with observable network traffic and configure exceptions.
Tuneup
Clean junk files and delete invalid registry/disk entries within the network for enhanced performance of endpoints.
Multiple Update Managers
Multiple update managers can be deployed to achieve load-balancing and to avoid network congestion caused by a single update manager.
Roaming Platform
Cloud-based solution that allows enterprises to manage endpoints at all times, even when they are out of the network. Admins can view the latest status, apply policies, redirect clients and maintain compliance.
Email and SMS Notifications
Notifications about critical network events can be preconfigured to reach appropriate parties via email or text messages.
Endpoint Security Business
Endpoint Security Business provides advanced and easily deployable protection for business enterprises. This unified suite is designed to safeguard endpoints on all platforms without compromising high-level performance.
Key Benefits
- Advanced endpoint protection with antivirus, intrusion detection, firewall and more.
- Proactive scanning of installed applications to detect unforeseen vulnerabilities.
- Detailed insights into every connected endpoint for uniform asset regulation.
- Uninterrupted protection against malicious websites, phishing attacks and more.
Features of Endpoint Security Business
Asset Management
Vigilant monitoring of hardware and software configurations of every endpoint allows administrators to stay in-the-know of any alterations on company systems.
Vulnerability Scan
By scanning known vulnerabilities of applications and operating systems, this feature allows users to update necessary security patches.
Data Loss Prevention*
Secures confidential data and prevents the leakage of business secrets to avoid losses. Data-at-rest can also be scanned on endpoints and removable devices.
IDS / IPS Protection
Advanced protection that pro-actively detects and prevents malicious activity which may exploit application vulnerabilities.
Group Policy Management
Administrators can define user groups based on the hierarchy within the organization and set flexible policies as per situational requirements.
Browsing Protection
Endpoint clients can be safeguarded against attacks originating from malicious websites accessed from within the network.
Phishing Protection
Phishing attacks that originate from malicious codes over the Internet are thwarted before they can enter the network and spread.
Firewall Protection
Administrators can customize permission-based rules in line with observable network traffic and configure exceptions.
Multiple Update Managers
Multiple update managers can be deployed to achieve load-balancing and to avoid network congestion caused by a single update manager.
Email and SMS Notifications
Notifications about critical network events can be preconfigured to reach appropriate parties via email or text messages.
Compare Products
| Features | EPS - Business | EPS - Total |
|---|---|---|
| Antivirus | ||
| Email Protection | ||
| IDS/IPS Protection | ||
| Firewall Protection | ||
| Phishing Protection | ||
| Browsing Protection | ||
| SMS Notification | ||
| Vulnerability Scan | ||
| Asset Management | ||
| Spam Protection | ||
| Web Filtering | ||
| Application Control | ||
| Advanced Device Control | ||
| Tuneup | ||
| File Activity Monitor | ||
| Roaming Platform |
UTM(Unified Threat Management)
As small or medium business cannot afford to deploy all the different standalone security solutions an Enterprise would deploy. Not only is there a large capital outlay but the operational costs and staff required would divert valuable resources away from growing the business. Hence there is a balance between cost and complex features which are sometimes never used. Network Security is the foundation of any security strategy but this also needs complimenting by Endpoint, Application, Access and Security Management.
TERMINATOR (UTM)
A one-stop solution for all enterprise security needs. With the UTM appliance as your first line of defense, your network is secure and your employees can focus solely on productivity and business impact.
Features of TERMINATOR (UTM)
Gateway Antivirus
Scans all incoming and outgoing network traffic at the gateway level. Augments existing virus solutions by reducing the window of vulnerability (WoV).
IDS / IPS
Scrutinizes network traffic in real-time and forestalls a broad range of DoS and DDoS attacks before they penetrate the network.
Firewall
Admins can permit or block access for traffic between internal and external networks based on enterprise compliance policies.
Gateway Mail Protection
Scans incoming/outgoing emails or attachments at the gateway level to block spam and phishing emails before they enter the network.
Load Balancing
Allows the distribution of bandwidth across multiple ISPs within the enterprise network and enables these ISPs to operate over the same gateway channels.
Automatic Link Failover
Shifts network load from inactive ISP lines to active lines in order to reduce Internet downtime and streamline the transition.
Content Filtering
Allows blocking of non-business related web traffic including streaming media sites, downloads, instant messaging etc. in order to reduce unnecessary load on enterprise bandwidth.
VPN
Provides IT administrators with a means for secure communications between the company's remote users and for building site-to-site connections.
Bandwidth Manager
Allows the allocation of enterprise bandwidth on the basis of individual users or user groups.
IT Policy Management
Provides comprehensive logging and reporting with a user-friendly web-based configuration.
Key Benefits
Business Benefits
- IT security management
- Safe working environment
- High productivity
- Regulatory compliance
- Cost-effective bundled solution
Financial Benefits
- Consolidated cost-effective solution
- Optimum use of IT resources
Technological Benefits
- Cumulative network security
- Plug-and-play solution
- Extensive support for your Seqrite TERMINATOR
Cyberoam (UTM)
Cyberoam Unified Threat Management hardware appliances offer comprehensive security to organizations, ranging from large enterprises to small and branch offices. Multiple security features integrated over a single, Layer 8 Identity-based platform make security simple, yet highly effective. Cyberoam's Extensible Security Architecture (ESA) and multi-core technology carry the ability to combat future threats for organizations' security.
Cyberoam’s NG series UTM appliances offer future-ready security with best-in-class hardware, along with software to match, to offer up to 5 times the industry average throughputs, making them the "fastest UTM appliances" for SOHO/ SMB segments. The FleXi Ports (XP) available in NG Series appliances starting with CR200iNG-XP offer organizations the network flexibility and configuration freedom with I/O slots that allow choice of Copper GbE and Fiber 1GbE/10GbE network connectivity.
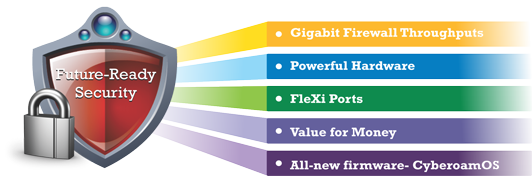
Gigabit Firewall Throughputs
The NG series appliances deliver the best in class Firewall and UTM throughputs.
Powerful Hardware
The NG series appliances come with a powerful hardware consisting of Gigahertz processors for nano second security processing along with Gigabit Ethernet ports and high port density. A complete overhaul of the appliance design has resulted into an unmatched performance gain with next-generation memory and more storage capacity.
FleXi Ports (XP)
The FleXi Ports in NG Series appliances offer flexible network connectivity with I/O slots that allow additional Copper/Fiber 1G/10G ports on the same security appliance, allowing organizations to upgrade to new technologies easily and cost-effectively, making them future-ready. The FleXi Ports consolidate the number of devices in a network, offering benefits of power efficiency, reduced network complexity and reduced operational costs.
Wi-Fi security
We offers security over Wi-Fi with its Wi-Fi range of appliances that combine the features of a router and complete set of UTM features, offering reduced TCO to organizations. The appliances offer Layer 8 Identity-based security, allowing administrators to apply identity-based security policies to gain visibility over user activity in the Wi-Fi network. The appliances come with an in-built wireless access point featuring 802.11 n/b/g standards, MIMO technology and up to eight virtual access points.
Fortinet
As businesses grow, they add employees, offices, computing devices, and business applications. These all must be networked in order for individuals and information to be accessible—anytime anywhere—to serve customers, spur growth, and improve profitability. Wherever a business is on its growth path, Fortinet provides everything it needs—top-rated protection from network to end-user devices, integrated wired/wireless equipment, and a single pane of glass to easily manage it all. This comprehensive capability is integrated and easy to manage—and a key reason why Gartner views us as "setting the cadence for the UTM Market."

- Top-rated technologies protect users, systems, and data
- FortiGate UTM Appliances protect the edge, while FortiClient secures the endpoints
